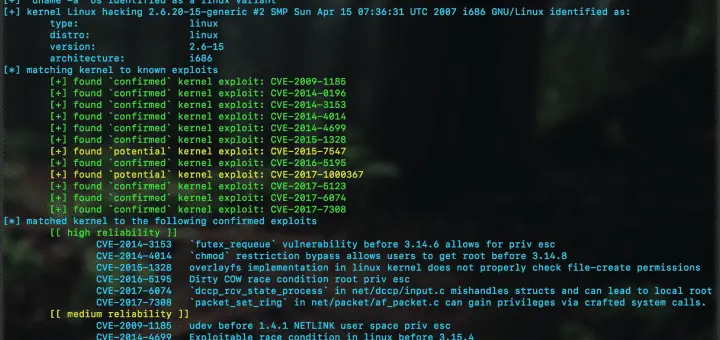
HackTheBox Write-Up — Nineveh. Nineveh is a machine vulnerable to… | by Bradley Fell, @FellSEC | Medium
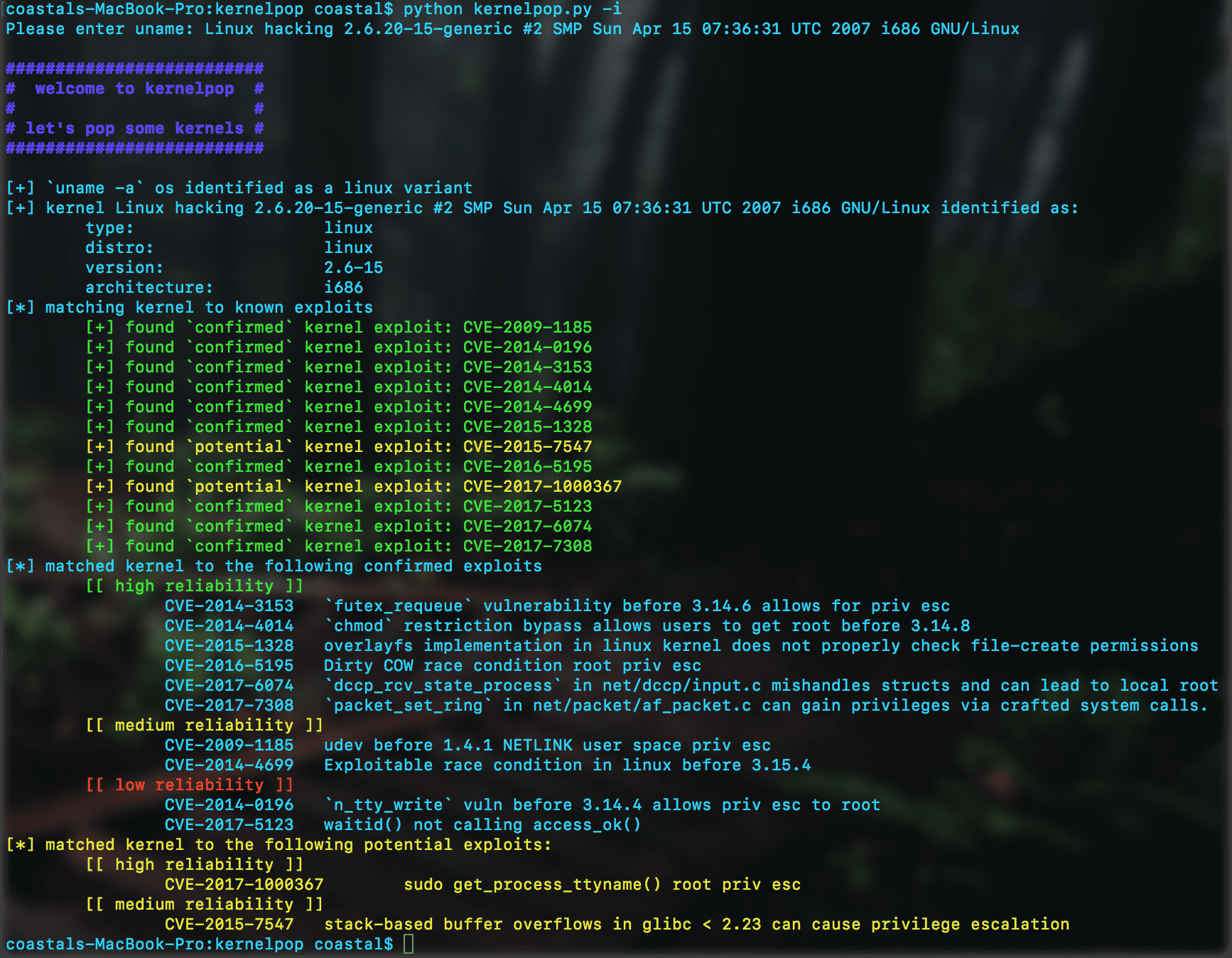
GitHub - jiayy/android_vuln_poc-exp: This project contains pocs and exploits for vulneribilities I found (mostly)
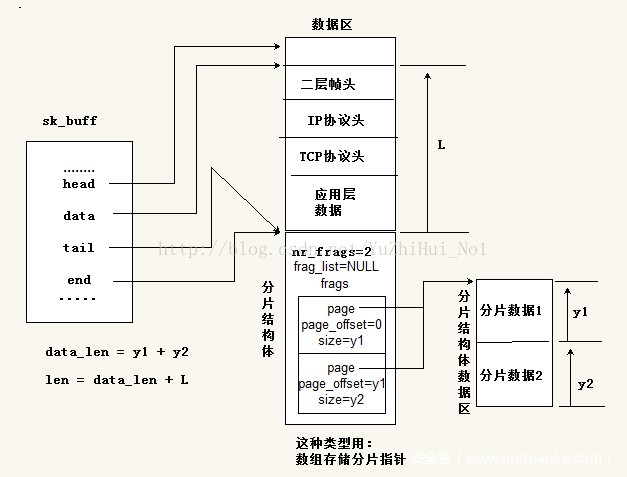
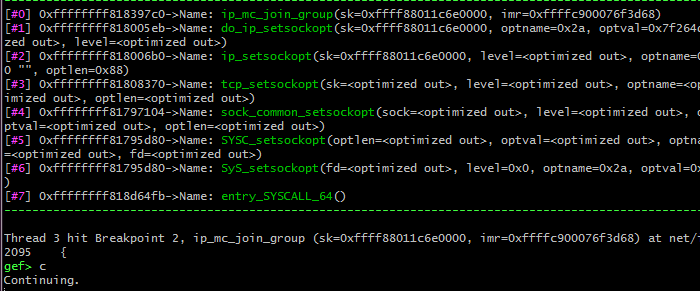
grsecurity-101-tutorials/kernel_vuln_exp.md at master · hardenedlinux/grsecurity-101-tutorials · GitHub

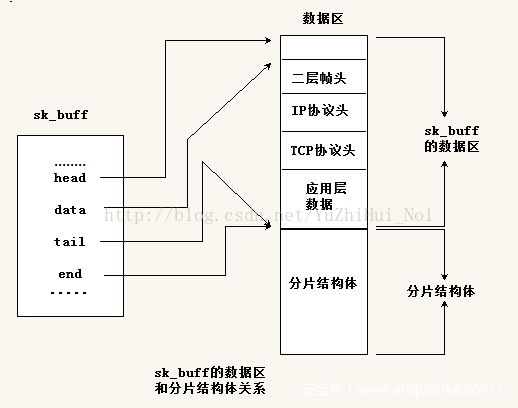
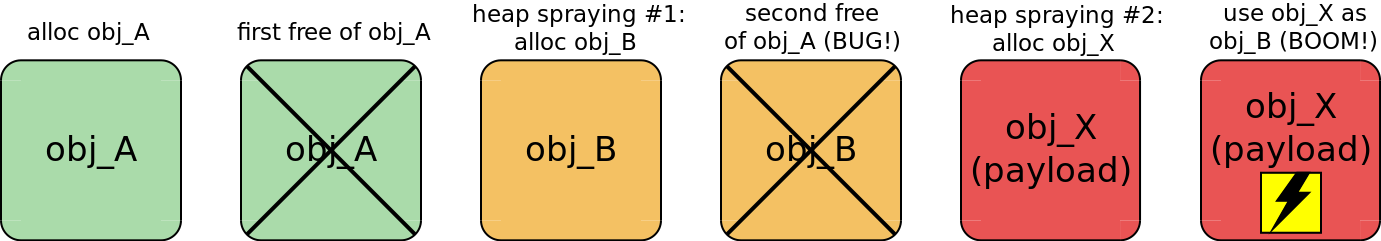
x0rz on Twitter: "CVE-2017-6074: DCCP double-free vulnerability (local root), works for #Linux >2.6.18, public PoC soon https://t.co/kdKlBKfrla #vulnerability https://t.co/GVUPm4agff" / Twitter